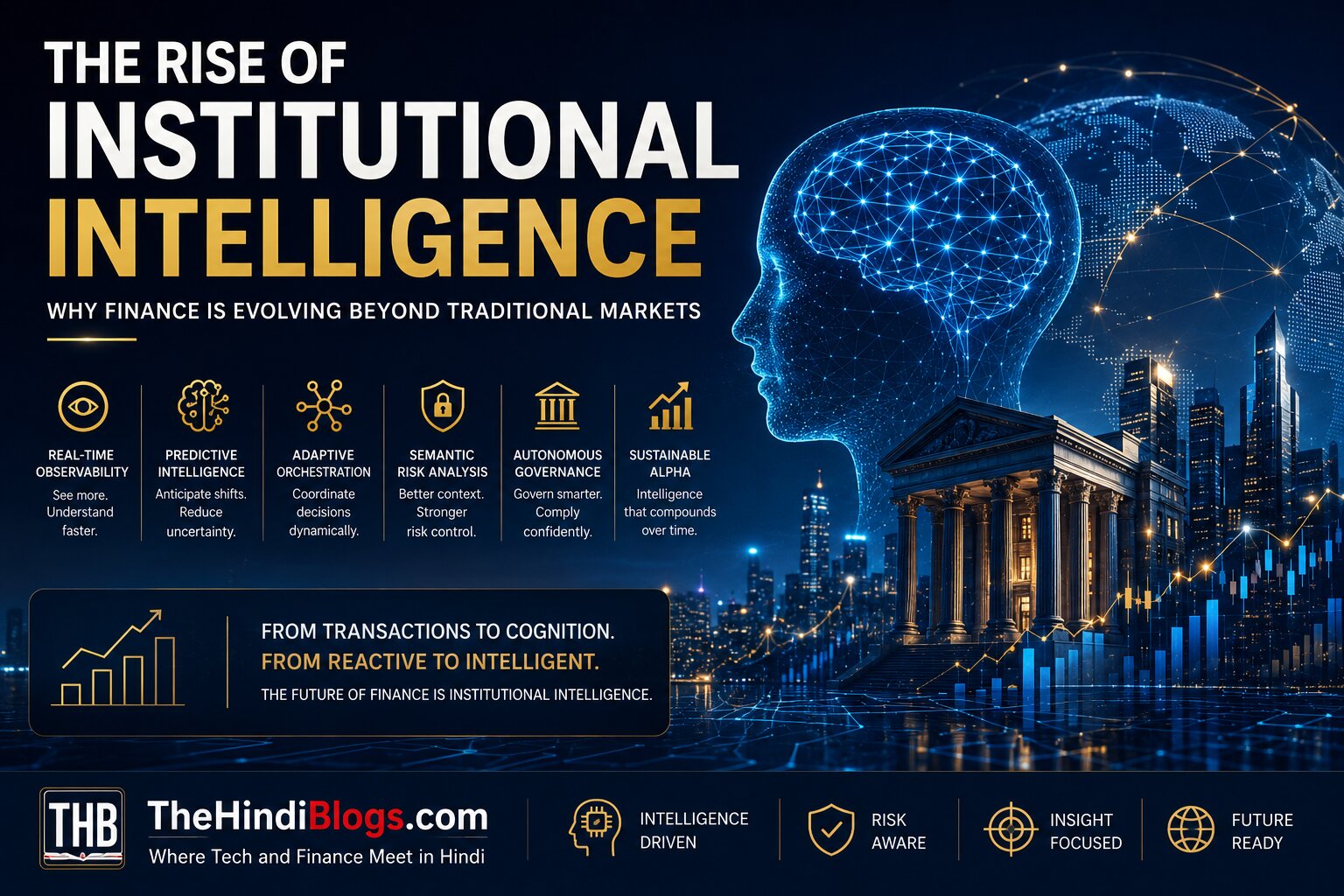
Global finance is entering a structural transition. For decades, financial institutions primarily optimized around: But modern financial systems are becoming exponentially more complex. Today’s institutions must continuously process: The challenge is no longer merely: managing capital. The challenge is increasingly: coordinating intelligence. This is creating the emergence of: Institutional Intelligence Systems. From Financial Infrastructure to Cognitive Finance Infrastructure Traditional financial infrastructure focused on: Modern financial infrastructure is evolving toward: Finance is becoming: cognition-native. Why Traditional Financial Systems Are Under Pressure Modern markets operate at: A single event can instantly affect:…
Read MoreAuthor: Ujjwal Singh Rathore
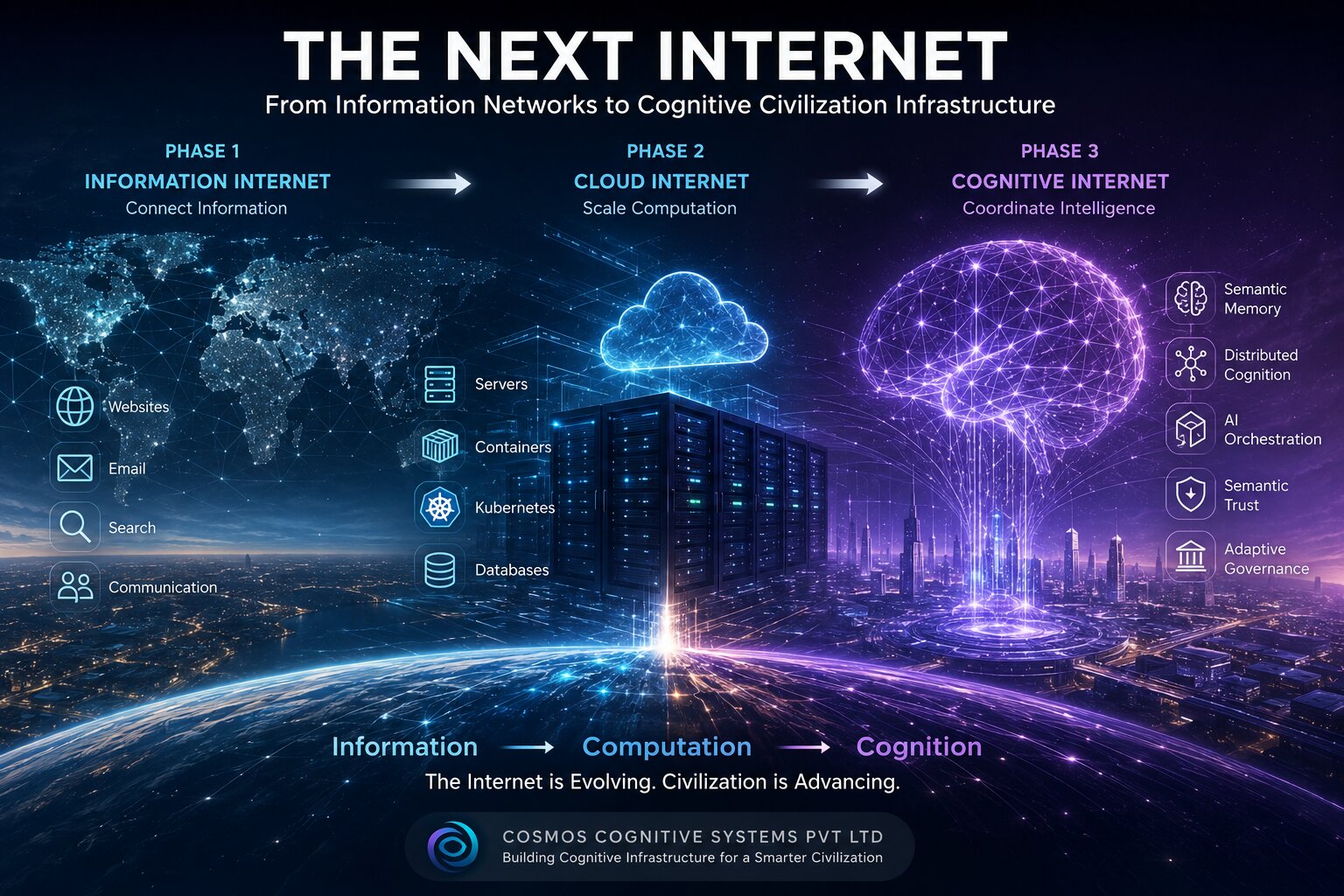
The Next Internet: From Information Networks to Cognitive Civilization Infrastructure
The internet began as a communication system. It evolved into a global information network connecting: Then cloud computing transformed the internet into a planetary execution layer capable of: Artificial intelligence accelerated this transition further. But a deeper architectural shift is now underway. The internet is evolving beyond: information infrastructure and beyond: cloud infrastructure toward: Cognitive Civilization Infrastructure. This may become one of the most important infrastructure transitions of the 21st century. Phase 1 — The Information Internet The first era of the internet optimized: information exchange. Core technologies included: The…
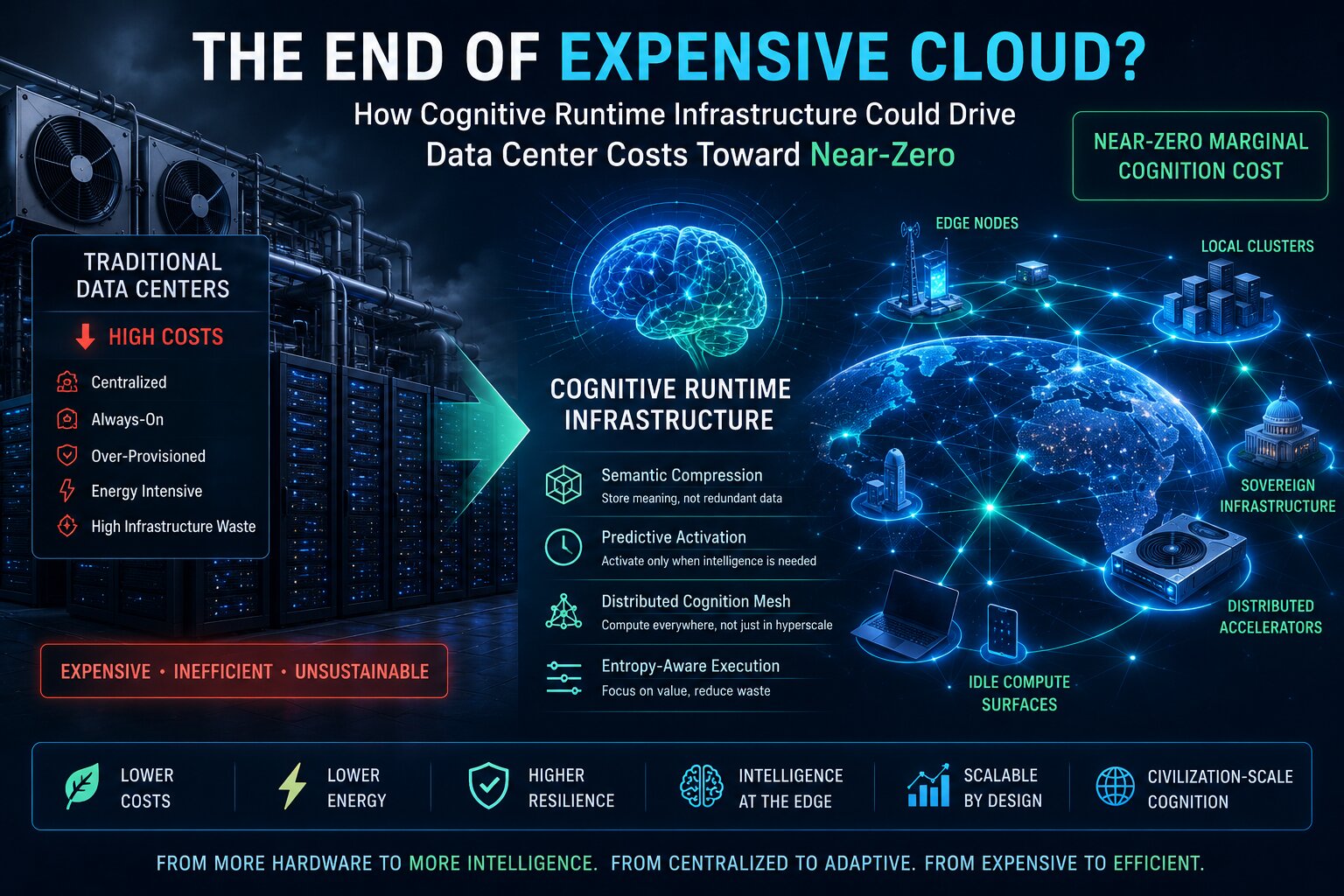
Read MoreThe End of Expensive Cloud? How Cognitive Runtime Infrastructure Could Drive Data Center Costs Toward Near-Zero
For two decades, modern computing has scaled through a simple assumption: More intelligence requires more infrastructure. More: This model powered: But a structural problem is now emerging. As artificial intelligence evolves toward: the infrastructure cost curve becomes unsustainable. The current trajectory leads toward: Civilization-scale cognition cannot scale linearly with hardware growth alone. A fundamentally different architecture is required. That architecture is beginning to emerge through: Cognitive Runtime Infrastructure. And its most important implication may be this: The future of intelligence may depend less on infinite compute and more on intelligent…
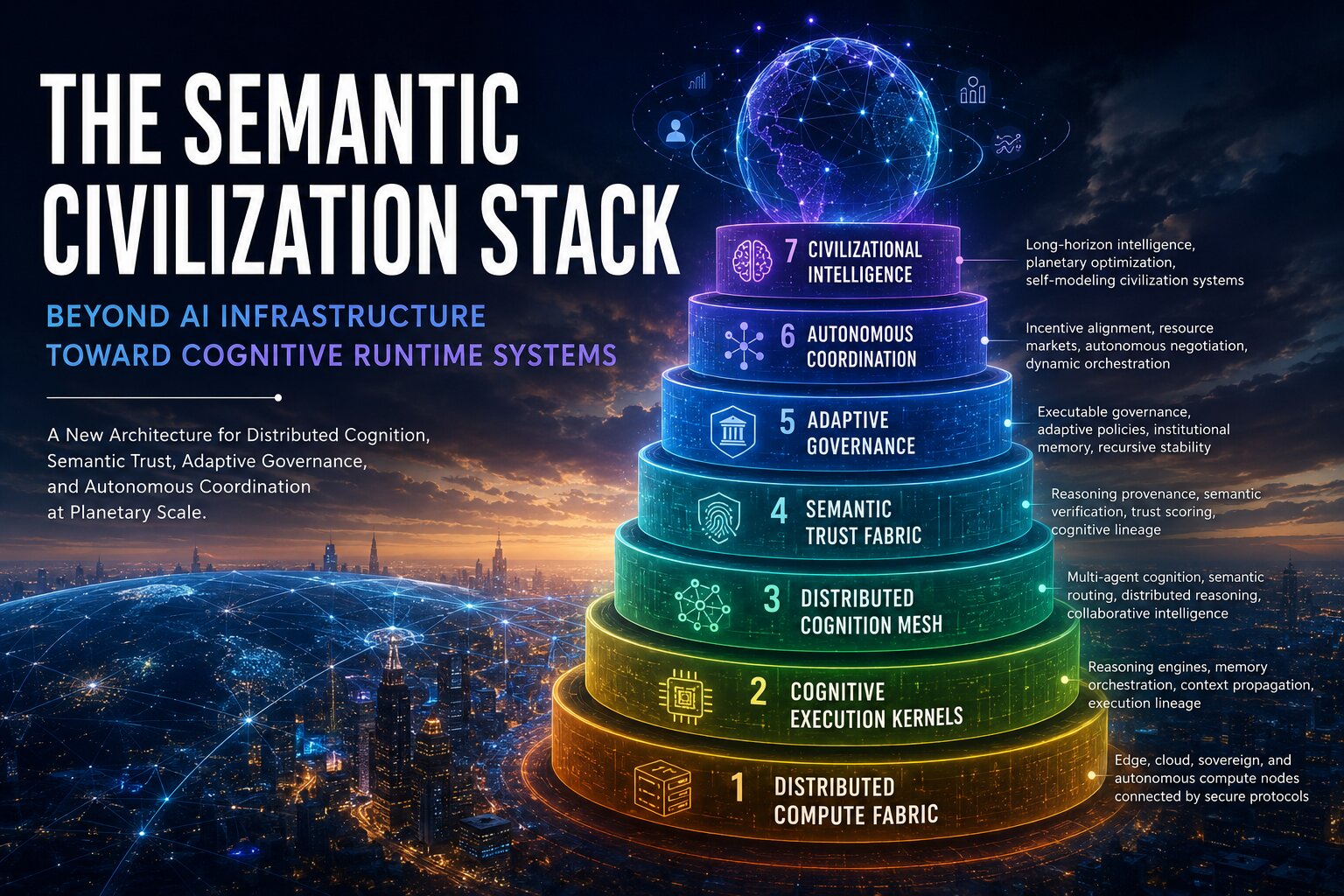
Read MoreThe Semantic Civilization Stack: Beyond AI Infrastructure Toward Cognitive Runtime Systems
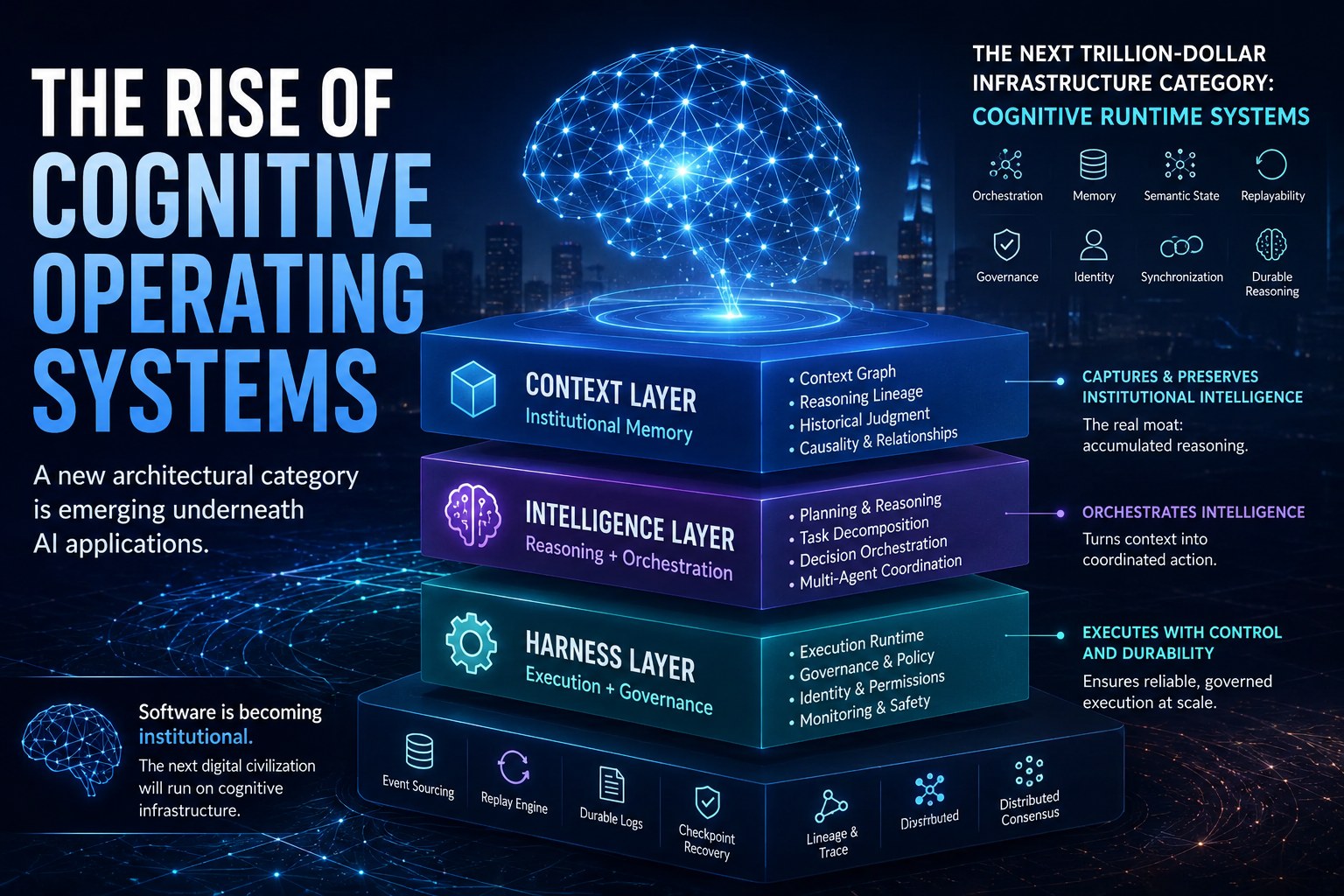
Artificial intelligence is no longer evolving as isolated models. A deeper architectural transition has begun. The first era of computing virtualized hardware.The second virtualized infrastructure.The third connected global information networks.The fourth introduced machine learning systems capable of pattern recognition. Now a fifth layer is emerging: Cognitive Runtime Infrastructure. Not software.Not merely AI.But continuously adaptive systems capable of: across institutions, infrastructures, and societies. Your earlier articles explored: The next evolution extends beyond both. We are entering the age of: The Semantic Civilization Stack. From Information Systems to Cognitive Systems Traditional software…
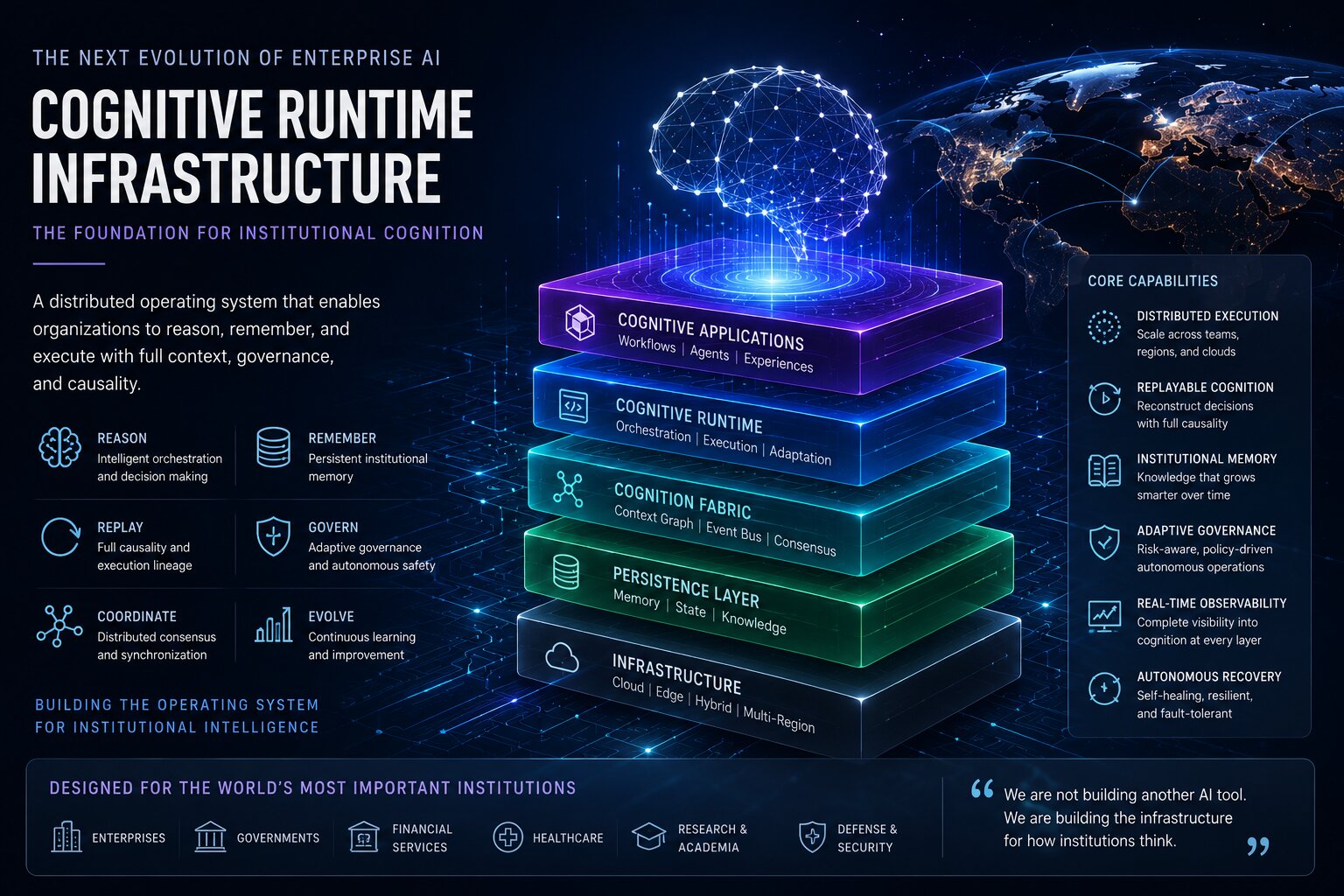
Read MoreThe Emergence of Cognitive Runtime Infrastructure
Artificial intelligence is entering a new architectural era. For the past several years, most AI systems have been designed as: These systems generate responses.They automate tasks.They accelerate productivity. But they still suffer from a foundational limitation: they do not preserve cognition across time. Most AI systems today are fundamentally stateless. They reason momentarily.Then forget. This is beginning to change. A new category of infrastructure is emerging: Cognitive Runtime Infrastructure This is not simply another AI platform. It represents the evolution of software infrastructure itself – from systems that execute applications…
Read MoreThe Operating System Era of AI Has Begun
Why the Future Will Belong to Cognitive Infrastructure, Not Chatbots Artificial intelligence is no longer the product. Infrastructure is. For the last three years, the world has been obsessed with models: That phase is ending. The next decade will not be defined by who has the smartest model. It will be defined by who builds the operating system underneath intelligence. The market is already showing the transition. The most advanced AI systems inside enterprises are quietly moving away from: toward: This is not an incremental shift. It is the architectural…
Read MoreWhat Are AI Agents? (LLMs vs Workflows vs Agents Explained Simply)
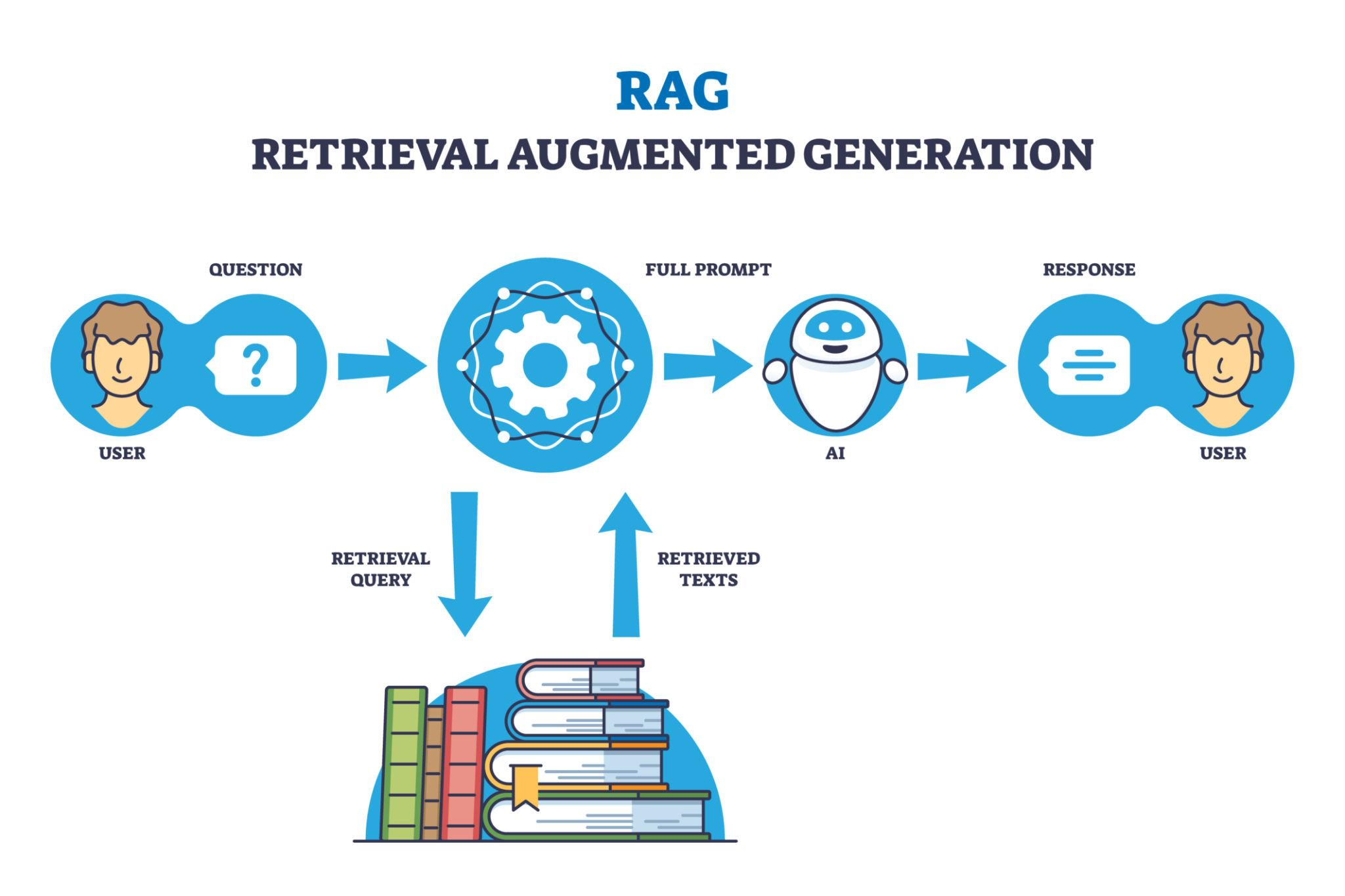
Introduction Artificial Intelligence is evolving rapidly, and terms like AI agents, workflows, RAG, and LLMs are becoming common. But most explanations miss one key idea: AI is evolving in three clear stages – from simple responses to fully autonomous systems. In this guide, you’ll understand: The 3 Levels of AI (Simple Framework) AI systems evolve in three levels: The difference between them is simple: Who is making decisions? Level 1: What Are LLMs? Large Language Models (LLMs) power tools like ChatGPT, Gemini, and Claude. How They Work Input → Model…
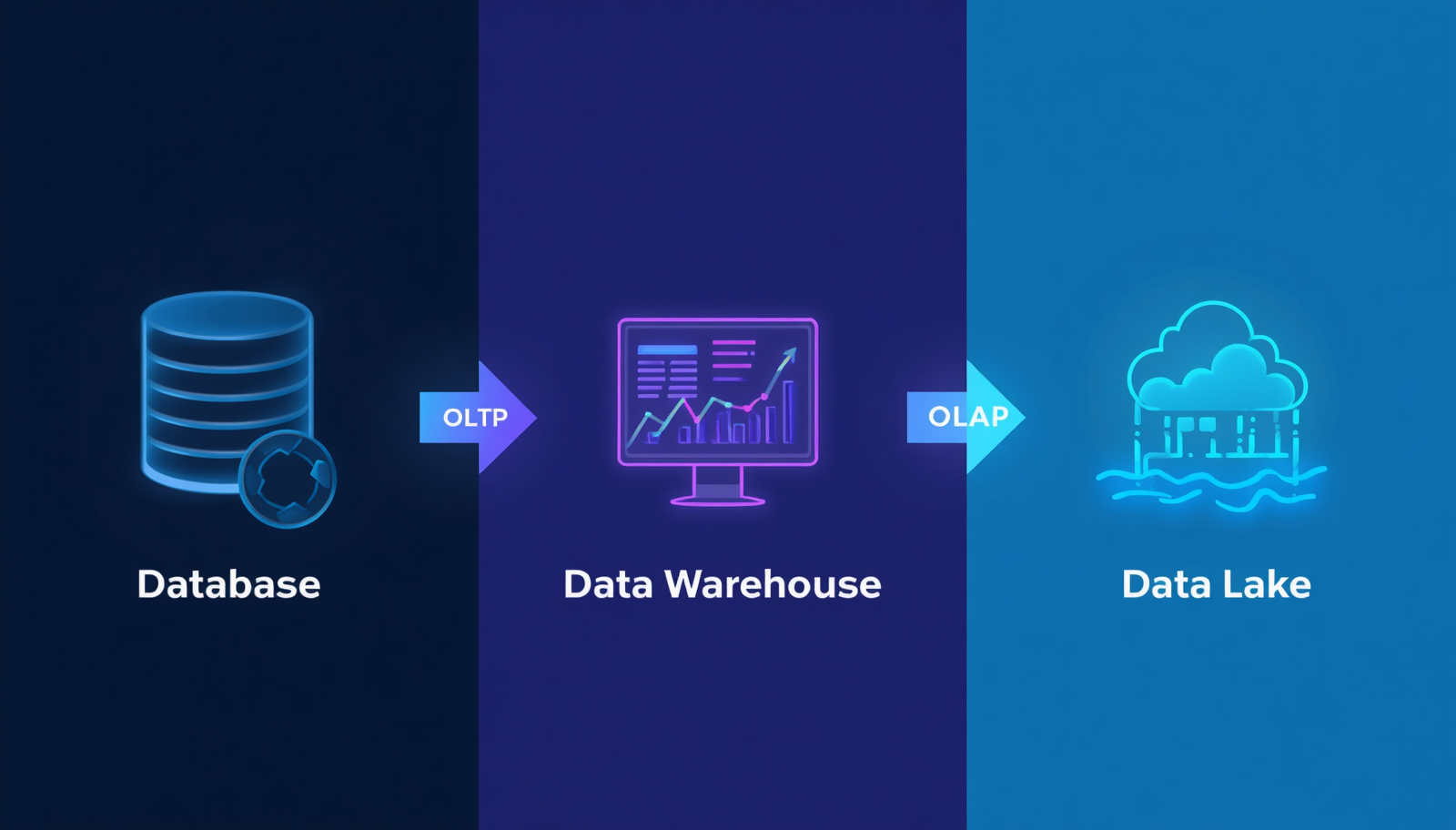
Read MoreDatabase vs Data Warehouse vs Data Lake: Complete Beginner’s Guide
Introduction When working with data, you’ll often hear three terms: At first, they can seem similar – but they serve very different purposes in modern data systems. Understanding these differences is essential if you’re working in data engineering, analytics, or AI systems. What is a Database? A database is used to store and manage real-time transactional data. As explained in the source , databases typically use OLTP (Online Transaction Processing) systems. Key Characteristics: Example Use Cases: Databases are optimized for writing and updating data quickly What is a Data Warehouse?…
Read MoreThe Ultimate Beginner’s Guide to RAG (Retrieval-Augmented Generation)
Introduction Artificial Intelligence is evolving rapidly, but one major limitation of Large Language Models (LLMs) is their inability to access real-time or private data. This is where Retrieval-Augmented Generation (RAG) comes into play. RAG is transforming how AI applications work by combining LLMs with external knowledge sources, enabling more accurate, relevant, and up-to-date responses. In this guide, we’ll break down RAG from scratch – covering concepts, architecture, and implementation. What is RAG? Retrieval-Augmented Generation (RAG) is a technique that enhances LLM outputs by retrieving relevant data from external sources before…
Read MoreAgentic AI Explained: From Simple Chatbots to Autonomous Intelligent Systems
Introduction AI is evolving rapidly – but not all AI systems are created equal. While many applications today use AI for answering questions or generating text, a new class of systems is emerging: Agentic AI These systems don’t just respond – they think, plan, and act. In this article, we’ll break down what agentic AI really is, how it differs from traditional AI systems, and why it represents the future of intelligent software. What is Agentic AI? Agentic AI refers to systems that can: In simple terms: Agentic AI =…
Read More